Governance for a
Sovereign Future.
Cryptographic evidence of every autonomous decision — committed before execution, immutable after finalization, independently verifiable by anyone.
The Premise
Frontier AI capability is now
too dangerous to deploy
without cryptographic accountability.
Anthropic's Mythos containment is necessary — but not sufficient.
AGTS is the missing accountability layer.
01 — Core Framework
Analytical Architecture
Semantic Validity
G1 validates decision entropy. Scattered, uncertain reasoning is detected and blocked before the decision can reach execution. Coherence is mandatory, not aspirational.
Financial Validity
G2 validates coherence against regulatory threshold. Every financial commitment is gated on demonstrated reasoning alignment with applicable standards. No partial credit.
Operational Validity
G3 monitors energy expenditure. Runaway computational costs, resource abuse, or excessive optimization cycles are caught and blocked before they materialise as institutional risk.
02 — The Governance Loop
Five Gates. Three Leaves.
One Permanent Record.
Every AGTS governance cycle produces three canonical leaves: an authorization record, an execution trace, and a variance record. Together they answer the only question that matters: did the system do what it was authorized to do?
Semantic Validity
H ≥ 0.40Validates decision entropy against threshold. High-entropy decisions — scattered, uncertain reasoning — are blocked before execution.
Financial Validity
C ≥ 0.40Validates coherence score against regulatory threshold. Every financial commitment is gated on demonstrated reasoning alignment with applicable standards.
Operational Validity
E ≤ 0.60Monitors energy expenditure of the decision process. Runaway computational costs, resource abuse, or excessive optimization cycles are caught and blocked.
Policy Admission
EVIDENCE CLASSValidates that all four evidence artifact hashes are present and the evidence classification is valid (HOOKED, ATTESTED, or INSTRUMENTED). No unclassified or self-reported evidence is admitted.
Cryptographic Finalization
Ed25519 · MERKLEEd25519 signature and Merkle tree admission. The governance decision becomes a permanent, independently verifiable leaf in the append-only transparency log.
03 — Security Architecture
Separation of Power by Design.
No single actor can both authorise an action and suppress the evidence of that action. AGTS splits authority across four independent layers — each controlled by a different entity, each independently auditable.
Sovereign Authority
Hardware-backed signing on a dedicated secure element (HSM / TEE). Without the counter-signature, the leaf is not admitted.
Validator Quorum
3-of-4 Byzantine fault-tolerant quorum. Validators attest that the bundle is well-formed and gate-complete — they cannot change gate outcomes.
Independent Witnesses
External parties verify the log's append-only consistency. History cannot be rewritten without witnesses detecting the inconsistency.
Every leaf is a governance decision, permanently verifiable by anyone with a SHA-256 implementation.
Unbroken chain of governance decisions, each cryptographically linked to its predecessor.
Byzantine fault-tolerant. 3-of-4 quorum certificate required per leaf.
Every other system records what happened after execution. AGTS proves authorisation existed before.
04 — Protocol Architecture
The Accountability Protocol.
Just as TCP/IP provided a common language for computers to communicate, AGTS provides a common language for autonomous systems to be governed and audited.
| Protocol | Standardises | Layer | Controls |
|---|---|---|---|
| TCP/IP | Packet transmission | Network transport | How computers communicate |
| HTTP | Document transfer | Web content | How content moves |
| SWIFT | Financial messaging | Bank instructions | How banks coordinate |
| Visa / MC | Card authorisation | Consumer payments | How merchants get paid |
| AGTS | Governance obligations | AI commitment verification | Who authorised what, when, with what evidence |
The Great Inversion
TCP/IP inverted telecommunications: centralized circuit-switched networks became decentralized packet-switched networks. AGTS performs a similar inversion — separating execution from governance and making authorization independently verifiable.
Air Traffic Control
AGTS provides accountability infrastructure for autonomous systems, much like air traffic control ensures safe operation of aircraft. A clearinghouse recording obligations between autonomous systems.
05 — Certificate Transparency + Machine Governance
The Transparency Mesh.
Built on Certificate Transparency (RFC 6962). Log, Validators, Monitors — each independently operated, each cryptographically bound, whispering to form consensus across jurisdictions.
Node Registry
Fault Tolerance: 1
Regions: US · EU · UK
Hardware-backed ECDSA on a dedicated secure element (HSM or TEE). The Sovereign Authority counter-signs every governance envelope. Without the seal, the leaf is not admitted to the log. The private key never leaves the secure element.
Four validators — Customer, Auditor, Regulator, Independent — each with their own ECDSA key pair, each in a different jurisdiction. 3-of-4 BFT quorum required, with mandatory representation from at least one regulator and one auditor.
Independent monitor workers poll the transparency log, verify Signed Tree Heads, sample inclusion proofs, and gossip with peers. If the log equivocates — presents different views to different parties — the monitors detect it.
Clearinghouse Lifecycle
From Obligation to Proof.
Every governance decision follows the same deterministic path — ten stages, each producing a named, hashable, independently verifiable artifact.
06 — Federated Infrastructure
No Central Server.
No Single Point of Failure.
Every worker runs at the edge. Validators, monitors, and logs are independently operated across jurisdictions. L3 deploys dedicated infrastructure. L4 adds required witness quorums and cross-institution governance — the protocol is the same, the infrastructure is theirs.
Shared Platform · L1–L2
Dedicated · L3 Transparent
Networked · L4
Same protocol. Same gates. Same cryptographic guarantees. L3 and L4 deploy their own infrastructure — the governance standard is shared.
07 — Beyond Logging
A Governance Operating System.
Not a Dashboard.
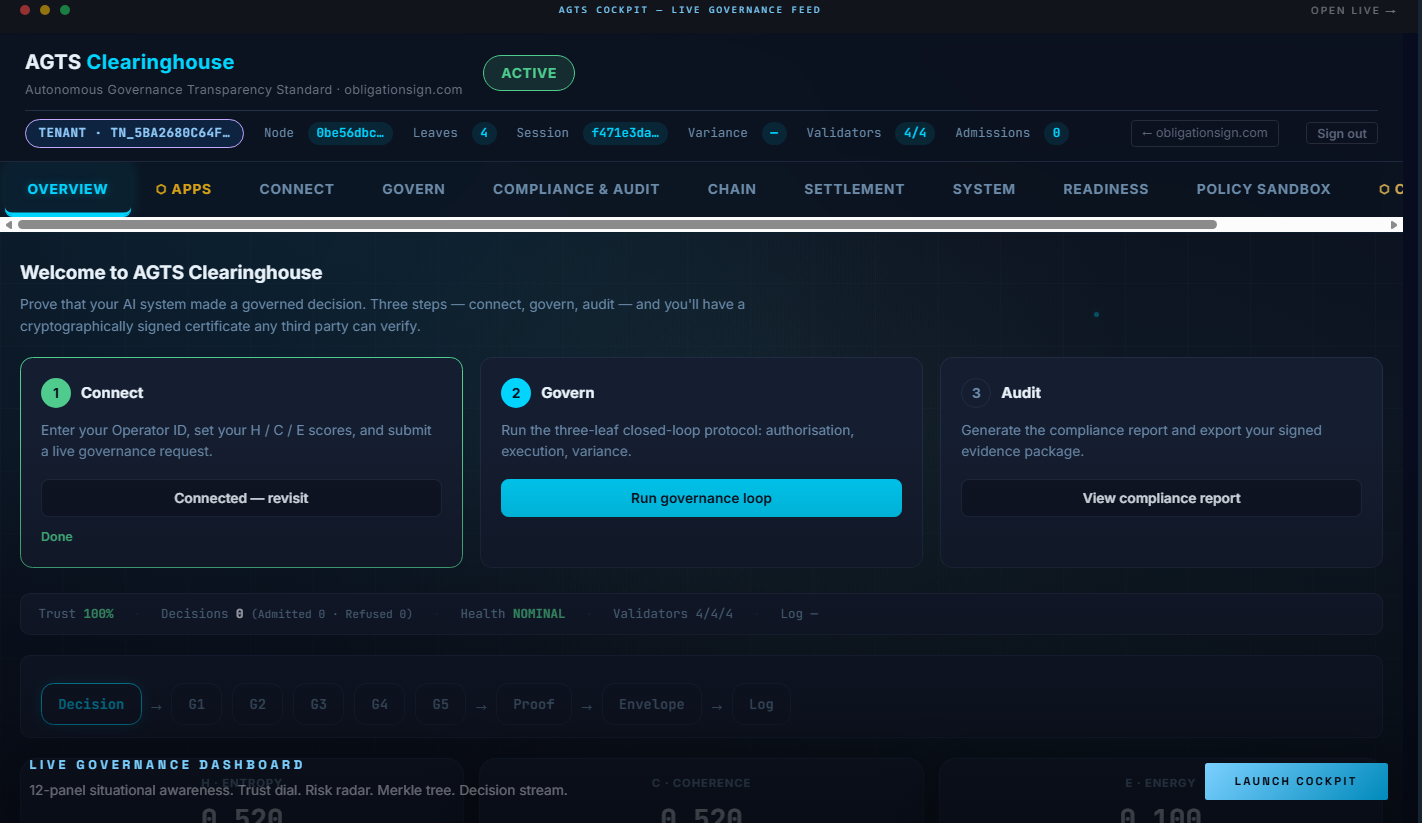
12-panel situational awareness.
Trust dial, risk radar, 3D validator topology, live decision stream, gate evaluation grid, Merkle tree panel — all updating in real time from live governance decisions.
Two replay systems. One for events. One for state.
Play back at 1x, 2x, 4x, or 8x speed. Step through trust scores and gate outcomes at any point in history. Time-travel debugging for governance.
Five axes. Three observables. Real-time risk surface.
Maps H, C, E, Gate Consensus, and Validator Quorum onto a live spider chart. When any axis contracts, you see it before it becomes a problem.
Three domain gates. Infinite extensibility.
Semantic (G1), Financial (G2), and Operational (G3) are domain-specific plugins — each providing its own evidence while inheriting the full governance pipeline.
08 — Domain Verticals
One Protocol.
Any Domain.
AGTS is domain-agnostic. A plugin translates domain-specific evidence into the five-gate structure. The same clearinghouse, same canonical leaf format, same transparency log — across every vertical.
Supply Chain
Cryptographic chain of custody for physical goods. Track provenance, prove authenticity, govern autonomous supply decisions with Merkle-anchored evidence.
Explore Vertical →Financial Services
Governance infrastructure for autonomous trading and financial commitment decisions. Every obligation — hashed, signed, anchored, and auditable.
Explore Vertical →Cybersecurity
Semantic governance for AI workloads — the layer NGFWs cannot reach. Govern autonomous threat response, model authorization, and incident remediation.
Explore Vertical →Critical Infrastructure
Governance for autonomous vehicles, robotics, and industrial control. Every actuator command, every control loop decision — cryptographically governed and proven.
Explore Vertical →09 — Sovereign Products
Same Protocol.
Your Infrastructure.
AGTS-governed products that prove their own behavior. Every session, every file, every message — cryptographically anchored to the same transparency log.
Sovereign VPN
Your VPN says it doesn't log. Ours proves it.
Cryptographic accountability for encrypted tunnels. Every session produces a birth leaf and death leaf — hashed, sealed, and anchored. Governance, not promises.
Sovereign Drive
They encrypt your files. We prove they can't read them.
Client-side AES-256-GCM encryption with P-384 ECDH key exchange. Every upload, share, and deletion anchored to the transparency log. Zero-knowledge storage.
Sovereign Mail
They promise encryption. We prove delivery, reading, and deletion.
End-to-end encrypted messaging with ECDH P-384 key exchange and Merkle-anchored provenance. Every message lifecycle event — delivery, read, delete — is a transparency log leaf.
MCP Gateway
They let agents call tools. We govern every invocation.
Model Context Protocol server for AI agents. 16 governance-gated tools across mail, drive, and VPN. Every tool call pre-authorized through five-gate evaluation, Ed25519-signed, and Merkle-anchored.
Start Governing
Your AI Today.
72-hour trial. 5 canonical leaves. Full Cockpit access. No credit card required. Every trial leaf is cryptographically identical to a production leaf in the same shared log.